Virtualization is revolutionizing the entire IT landscape. Simply put, it allows a physical object to be transformed into its logical “virtual” version. Virtualizing our IT resources reduces operational and capital expenses, it minimizes downtime, it allows faster provisioning, and the list goes one. The best example of this virtualization revolution is clearly on computing. Taking a server and creating a VM-version of it, allowed IT admins to consolidate hundreds of virtual servers into a single box. This “computing virtualization” opened the doors to cloud computing. The same that happened to compute, is now happening to other areas of IT, such as security and especially networking. Over the past couple of years, Network Function Virtualization (NFV) has become an increasingly popular solution for various networking challenges to a plethora of different companies operating within a wide selection of different industrial and commercial sectors. In previous articles, we have covered vCPE as the most popular use case of NFV, this article focuses more on other examples of NFV.
Network Virtualization: NFV and VNF
Before going deep into the examples of NFV use cases, let’s clarify two important concepts in network virtualization, NFV and VNF. One of the technologies that use the concept of IT virtualization, is Network Function Virtualization (NFV). This technology virtualizes full classes of network node functions and creates building blocks that link together to allow different networking services. NFV is allowing enterprises to design, provide, and ease into much more advanced services and operations as well as reduce outgoings through cost savings. NFV runs the software-defined network functions which are independent of the hardware platform. This concept is the key to understand the difference between NFV and VNF. NFV is the overall concept of running these network functions and the Virtualized Network Function (VNF) is its logical outcome. VNFs decouple software from the underlying hardware. These VNFs consist of VMs running software on top of NFV infrastructures (NFVi), such as generic hardware, virtual layer, or cloud infrastructure. 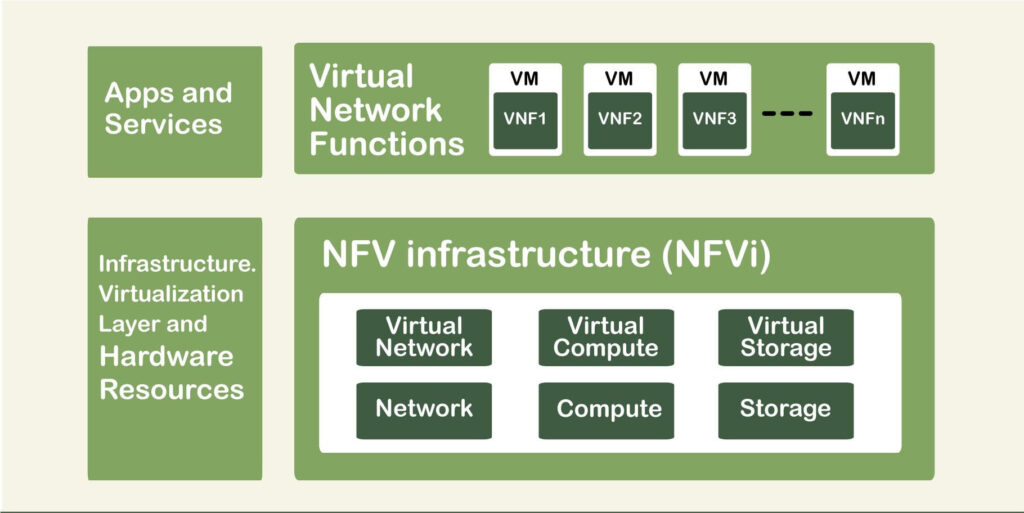
The clear benefit of this is to avoid using custom hardware devices for each network function. Load balancers, firewalls, IDS/IPS, and WAN accelerators can now run as a software function, without generic hardware.
Six Examples of NFV Use Cases
In this article, we’ve put together six examples of network function virtualization use cases that demonstrate how NFV is being used today to address a range of challenges as well as provide enhanced solutions to these and other networking hurdles in order to enhance services and reduce outgoings. So, let’s jump straight in.
Network Virtualization
The main use with which NFV technologies are being used by mainly telecom companies around the world is, of course, for network virtualization. As already discussed before, NFV separates the hardware from the software. The process creates a virtual network on top of the physical network. This decoupling of hardware and software allows service providers to expand and accelerate the development and innovation of services. It also helps to improve critical network requirements such as provisioning. In order to optimize their network services, consumers look to network virtualization to separate their network functions such as DNS, caching, IDS, and firewalling from the proprietary hardware that was, until recently, the dominant solutions. This solution also enables them to run on software instead. Network Virtualization gives service providers the agility and flexibility they need when rolling out new network services. It helps them reduce their spending on bulky physical hardware and the costs associated with running, maintaining, and occasionally repairing it. One of the best examples of network virtualization is the new MEC and SD-WAN. But, while network virtualization is one of the most popular applications of network functions virtualization, it is by no means the only one.
Mobile Edge Computing
Mobile edge computing is another technological innovation that has gone from strength to strength over the past couple of years. This technology looks like it is only gaining momentum as we carry on into the year 2020. While many people may ask, how do network function virtualization and mobile edge computing relate to one another? How are they especially related? In fact, they are indeed intrinsically linked and are actively influencing each other in both areas of development and the expansion of applications. Using network function virtualization allows edge devices to perform computational services and provide network functions by generating and utilizing either a single or multiple virtual machines (VM). Multi-Access Edge Computing (MEC) is a clear example of these technologies. The MEC is utilizing mobile edge computing to provide ultra-low latencies. This technology was born from the ongoing rollouts of 5G networks. The MEC uses individual components in its architecture which are similar to the NFV.
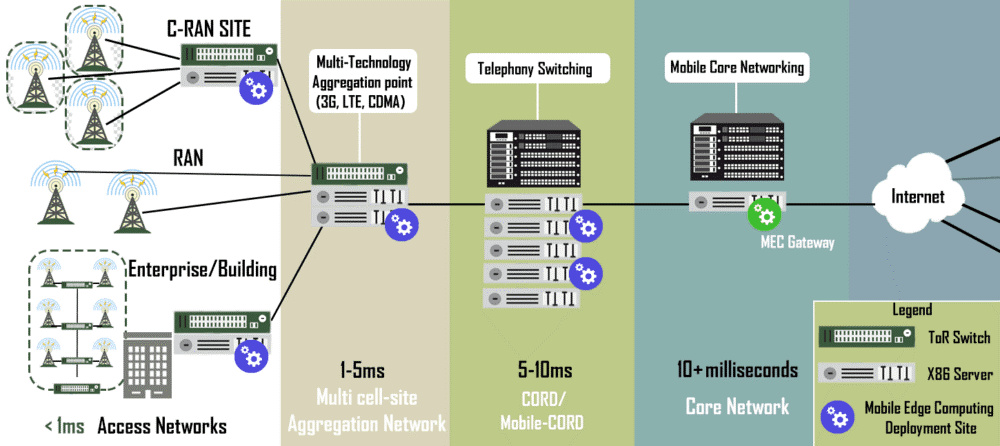
When it comes to “mobile”, edge computing refers to components such as radio towers, mini-data and local data centers. NFV takes some of these mobile network service functions and translates them from hardware to software. Network function virtualization, alongside other technological and network advances and developments such as software-defined networking and artificial intelligence, will likely become the prime solutions for the network challenges of tomorrow due to their early integration and combination with each other.
Orchestration Engines
One of the most beneficial NFV use cases is that of orchestration engines. With traditional legacy networks, issues such as low agility, human error, and lack of automatic processes and alerts made these kinds of networks extremely limited in their capabilities. One of the biggest causes of network downtime is human error. This is why automated systems are in such high demand. These systems also have the benefit of reducing the costs associated with paying for maintenance and upkeep as they require markedly less human intervention. NFV orchestration uses programming technology to manage the connections between network functions and services between The orchestration handles the NFVi and the VNFs. Centralized orchestration engines can prove to be an extremely worthwhile investment for those willing to get started, however, when considering a centralized automation engine, the following features are widely regarded as critical:
- Centralized policy automation
- Centralized hybrid WAN management
- Network-wide visibility and segmentation
- Public key infrastructure (PKI) certificate management
- Plug and play from day 0.
Video Analytics
Another technology that has seen a huge increase in its potential, since the inception of the Internet of Things, is video analytics systems and software. Now, companies are able to capture massive amounts of data using IoT video and smart devices installed in their factories, stores, offices, and even farms. But most of the time, high-performance AI video analysis is performed only cloud-native applications or powerful servers located on the cloud. So having to transfer these large amounts of data for analysis from on-premises to the cloud becomes a real challenge. The modern network usually faces an end-to-end network latency, which poses a real challenge for the apps and network services that are extremely sensitive to network delays, such as video analytics. In order to solve this challenge, enterprises have been turning to NFV and SDN architectures to reduce network resource utilization and improve latency. These technologies could when combined with using video analytics at the network edge, reduce bandwidth use by up to 90% according to some proposals. An example of this video analytics technology is a device like the NVA-3000 from Lanner. This device is an Enterprise-grade NVR for video surveillance/machine vision. Together with a low-latency network such as LTE or 5G, an NVR can gather video from multiple input channels such as video surveillance, it buffers it, pre-processes it and sends it over the network. The VNF provider sends network functions on-demand to the network edge.
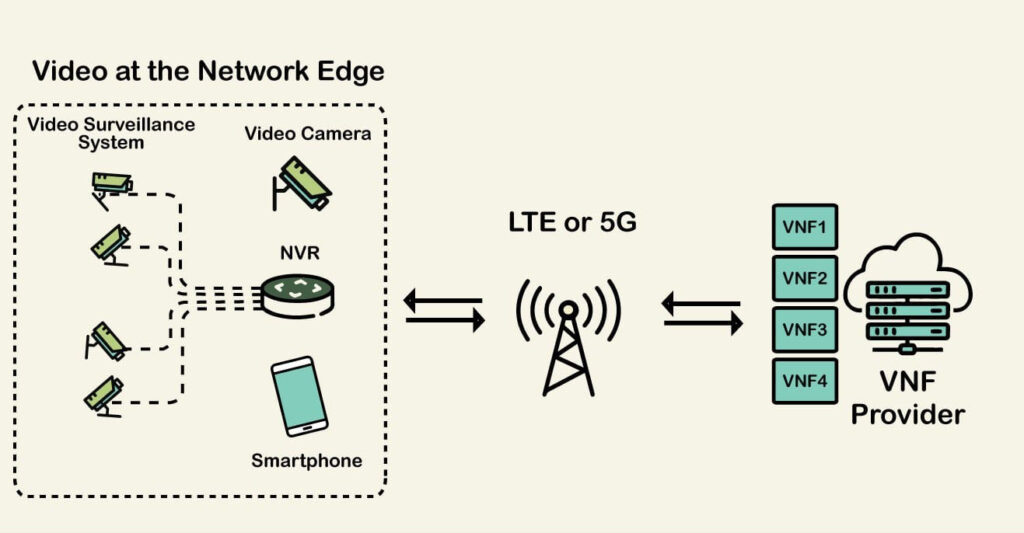
With IoT, smart, and edge devices enabling more and more data to be generated, collected, and then analyzed, video analytics systems and software have become and will continue to be an increasingly important part of utilizing the Big Data now available. Network functions virtualization is the architecture on which to build these systems.
Security
Just like the tools we use to farm our crops or manufacture our cars, the tools we use to protect our physical and virtual tools have evolved thanks to the various leaps in technological progress that have occurred over the last decade. Many security vendors are already offering virtual firewalls to protect VMs. The F5 Gi Firewall VNF Service, for example, is one of the most popular NFV solutions that encompasses firewall capabilities. But in reality, firewalls are just one of nearly every security device or component that will eventually be virtualized using network functions virtualization as well as software-defined networking. One of the main attractions to using virtualized security is the idea of centralized control mechanisms and equally distributed enforcement. These two benefits alone have seen companies looking to bolster their security flock to investigate these kinds of security solutions.
Network Slicing
Network slicing has gained a lot of popularity since the beginning of 5G design and rollouts. This technology aims to slice a physical network into multiple networks. NFV and Network slicing are two concepts very related and it is likely that NFV will begin to play a crucial role in this slicing, especially for 5G. Slicing the network is like creating sophisticated Virtual Private Networks (VPNs) and it can consist of a mix of physical and virtual instances. This technology creates multiple logical network instances throughout the same underlying physical network. Each instance or “slice” can be customized and optimized for different functions and allocated to specific departments. The slice is often provided as a VNF. The following Generic 5G Network Slicing framework proposed in “Network Slicing in 5G: Survey and Challenges” a journal published in IEEE, is based on three layers the service, network function, and infrastructure. The service layer (operator) pushes VNFs to the function layer that runs on generic hardware on-premises. The Orchestrator deals with the slicing for all these three layers.
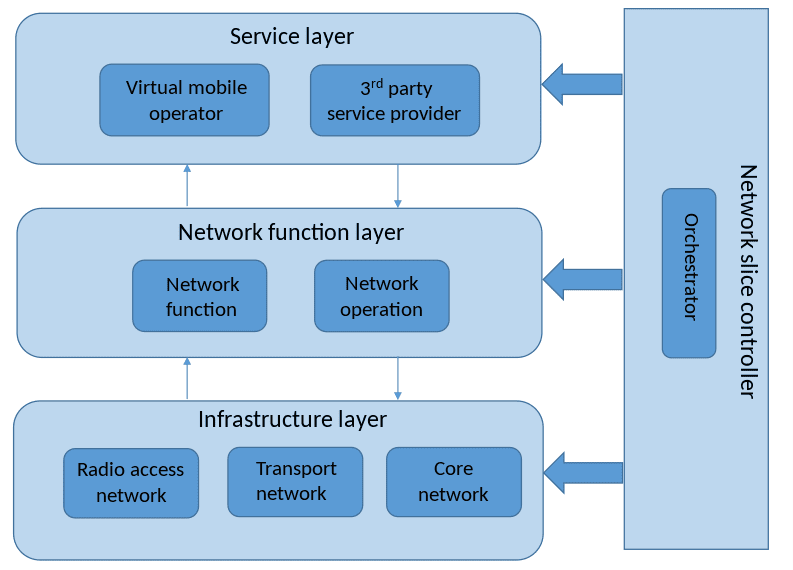
Since each slice of the network can be referred to as a network function, NFV will automatically allocate the necessary resources to each network slice at the right QoS and performance level. Some benefits of Network Slicing:
- Network slicing provides configurable and optimizes specific services.
- Adds flexibility, efficiency, and agility to the end-user.
- Reduces CapEx and OpEx.
- Improves deployment times for network services.
Final Words
Network function virtualization may not have quite conquered the world just yet, but, with the world becoming increasingly virtual and NFV (as well as SDN) gaining more and more momentum, we could soon see a day when virtual security, as well as the other use cases featured on this list, become the rule, rather than the exception.








